What Is a CI/CD Pipeline? Guide for Tech Leaders

Apr 17, 2026

Read in 8 Minutes
Table of Contents
- Introduction
- What Is a CI/CD Pipeline?
- How the Pipeline Works Stage by Stage
- Where a CI/CD Pipeline Delivers Real Business Value
- CI/CD Pipeline Architecture Patterns
- Tool Comparison Pricing and Use-Case Fit
- ROI of a Well-Built Pipeline
- Risks and Implementation Challenges
- Vendor Selection Checklist
- Top CI/CD Tools in 2026 Quick Reference
- Why Tibicle LLP Is Worth Considering for CI/CD Pipeline Implementation
- Conclusion
- Frequently Asked Questions About CI/CD Pipelines
Introduction
The global CI/CD tools market reached $1.73 billion in 2026 and is projected to climb to $4.53 billion by 2030, growing at a CAGR of 21.18% (Mordor Intelligence). That figure alone signals something important: a CI/CD pipeline is no longer a back-end engineering preference. It is a delivery infrastructure decision with direct and measurable consequences for release velocity, risk exposure, and engineering spend. At its core, it unifies continuous integration and continuous deployment practices into a single automated workflow.
For C-level leaders and engineering directors, understanding the mechanics and economics of a CI/CD pipeline is not optional. When pipeline architecture is misaligned with business requirements, the resulting slowdowns, failures, and security gaps show up in downtime costs, delayed product launches, and spiraling rework budgets.
This guide covers how a CI/CD pipeline works, what it costs, what it returns, and how to choose the right platform for your engineering organisation with the depth and specificity needed to make confident, informed decisions.
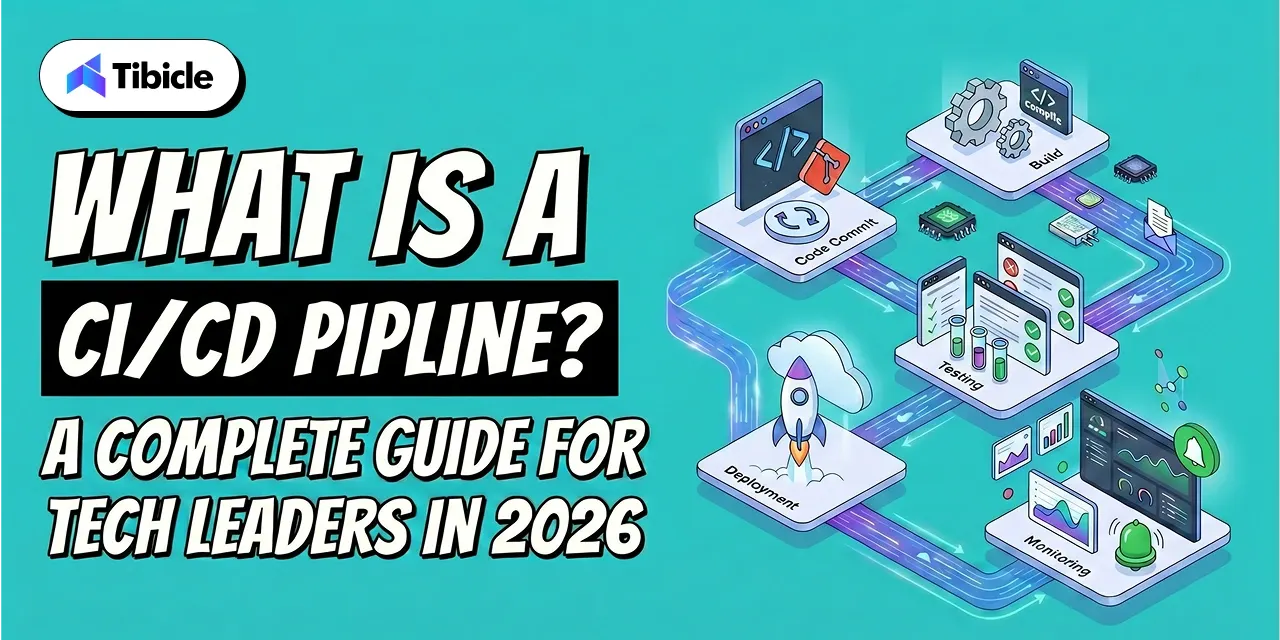
What Is a CI/CD Pipeline?
This pipeline is an automated sequence that moves code from a developer’s commit through building, testing, and deployment without manual handoffs at each stage. Indeed, it is the operational backbone of modern software delivery, eliminating the bottlenecks that accumulate when teams rely on manual processes between writing code and releasing it to users.
The term covers two distinct but interconnected practices: Continuous Integration (CI) and Continuous Delivery or Deployment (CD). Together, they form a pipeline that shortens the feedback loop between development and production, reducing both the cost and the risk of each release.
CI vs. CD in a CI/CD Pipeline:The Distinction That Affects Your Risk Model
The difference between CI and CD is not just technical it determines how much control your team retains at each release stage:
- Continuous Integration (CI): Every developer commit triggers an automated build and test sequence. Essentially, the goal is to detect integration errors immediately, before they compound. Failures are returned to the developer within minutes, not days.
- Continuous Delivery (CD): Code is always maintained in a deployable state. Builds that pass automated testing are queued for production release, but a human approval step remains at the gate. The team decides when to release the pipeline and handles everything up to that point.
- Continuous Deployment: The pipeline runs end-to-end without human intervention, including the final production push. As a result, every commit that passes all automated checks is deployed automatically. Naturally, this model requires high test coverage and mature monitoring.
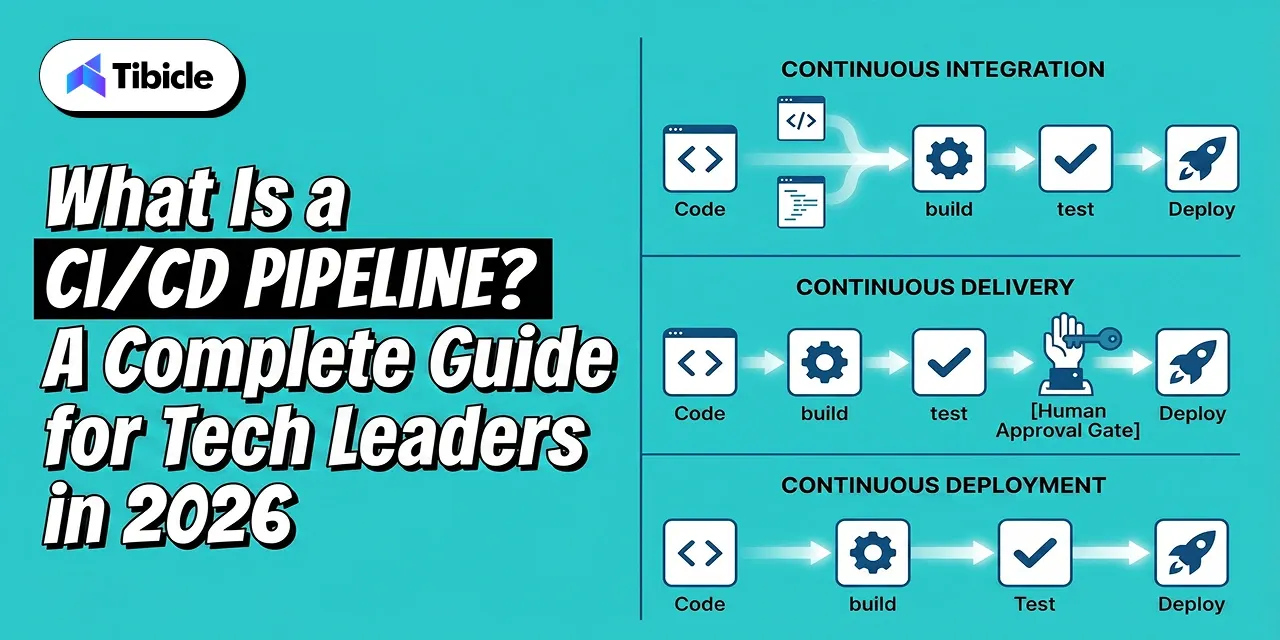
Ultimately, the choice between Continuous Delivery and Continuous Deployment is a governance question as much as an engineering one. Regulated industries, organisations with strict audit requirements, or teams launching high-stakes changes typically prefer the manual gate of Continuous Delivery. Continuous Deployment suits teams with high deployment frequency, strong observability infrastructure, and established rollback procedures.
How the Pipeline Works Stage by Stage
A CI/CD pipeline moves through five core stages. Each stage gates the next: a failure at any point halts the pipeline and returns feedback to the team, preventing defective code from advancing toward production.
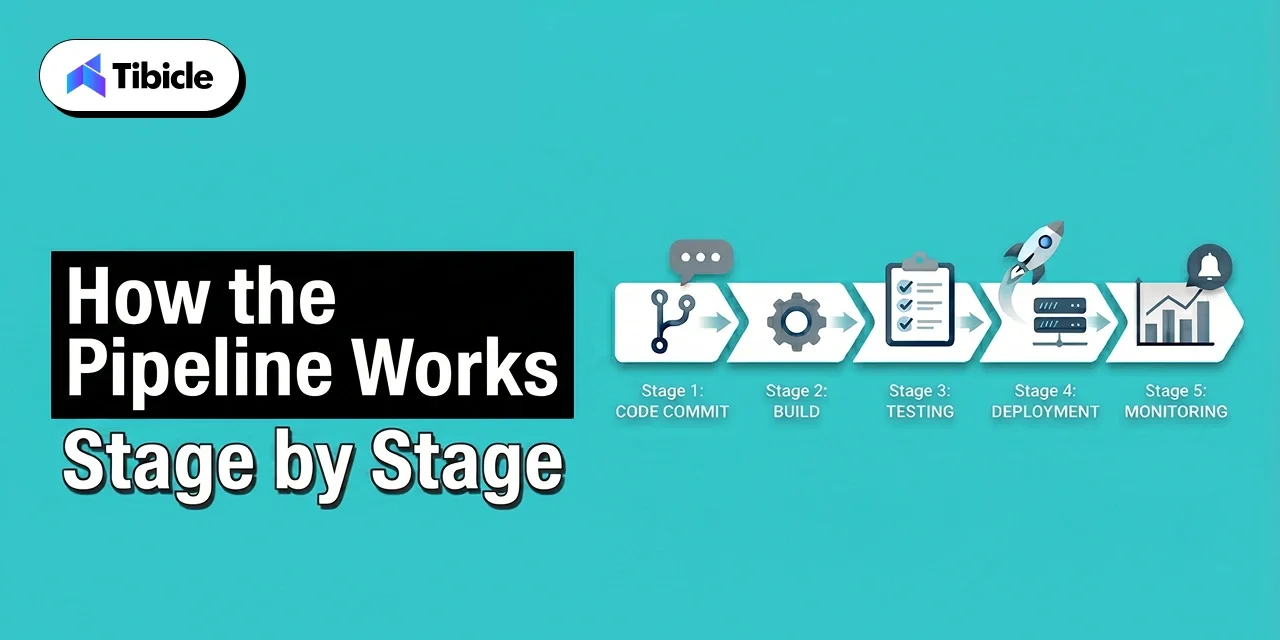
Stage 1: Source Control Trigger
Every commit or pull request fires the pipeline. Git serves as the entry point when a developer pushes code, the version control system notifies the CI/CD platform and the automated sequence begins. Additionally, branch protection rules and merge policies define which events trigger full pipeline runs versus lighter checks.
Stage 2: Build Layer
The build stage the foundation of build automation compiles source code, resolves dependencies, and packages deployable artefacts. This is where slow builds inflict real cost: a build layer that takes 20 minutes instead of 5 costs each developer 15 minutes of idle time per commit cycle. At scale, across a team running multiple daily commits, that idle time compounds into significant wasted engineering budget. Consequently, build caching, dependency pre-fetching, and parallelisation directly reduce this cost.
Stage 3: Automated Testing
Automated testing is the primary risk control mechanism in any CI/CD pipeline. Three levels operate in sequence:
- Unit tests: Fast, isolated tests validating individual functions or components. These run first because they provide the highest signal at the lowest execution cost.
- Integration tests: Validate that components interact correctly database connections, API calls, service-to-service communication.
- End-to-end (E2E) tests: Simulate real user flows through the full application stack. These run last because they are the slowest and most resource-intensive.
Pipeline failures at the test stage halt all downstream stages and immediately return feedback to the developer. Catching bugs here costs a fraction of what the same defect costs in production research consistently places production bug fix costs at 6 to 10 times higher than early-stage detection.
Stage 4: Deployment Stage
Once testing is complete, passing code moves to staging environments before production. Deployment strategies in a mature CI/CD pipeline include:
- Blue-green deployment: Two identical production environments run simultaneously. Traffic shifts from the old (blue) to the new (green) version, with instant rollback capability if issues arise.
- Canary deployment: New code rolls out to a small percentage of users first. Subsequently, traffic expands progressively as the system validates stability. Therefore, risk is contained to a subset of users during the validation window.
- Rolling deployment: Instances are updated incrementally, replacing old versions one at a time. No downtime, but rollback is slower than blue-green.
Stage 5: Monitoring and Feedback Loop
In addition, the pipeline integrates post-deployment with observability tools Prometheus, Datadog, or Grafana to monitor application health in real time. Moreover, anomalies, error rate spikes, and performance degradation can trigger automated rollbacks or alert on-call teams before users report issues. This closed feedback loop is what separates a mature CI/CD pipeline from a basic automation script.
Where a CI/CD Pipeline Delivers Real Business Value

The business case for a CI/CD pipeline is grounded in measurable operational and financial outcomes. Three specific data points frame the return:
Organisations with mature Continuous Delivery platforms deploy 208 times more frequently than low performers, according to the Puppet State of DevOps Report. Notably, deployment frequency is a proxy for competitive responsiveness; the ability to ship features, fixes, and experiments faster than rivals is a structural advantage.
Fixing bugs in production costs 6 times more than catching them within a CI/CD pipeline. Simply put, the earlier in the delivery cycle a defect is detected, the lower the cost of resolution. This is not a marginal efficiency, it is a material reduction in engineering rework cost.
Developer idle time from slow or broken builds is a hidden cost that most engineering budgets do not surface. When a developer waits 30 minutes for a build or spends three hours debugging a pipeline failure caused by configuration drift, that time appears as engineering headcount cost with zero productive output.
Industry-Specific Use Cases for CI/CD Pipeline Automation
For instance, different sectors prioritise different pipeline capabilities based on their regulatory environment and delivery requirements:
| Sector | Primary CI/CD Driver | Key CI/CD Pipeline Requirement |
| Fintech | Compliance + speed | Audit trails, policy gates |
| SaaS | Multi-environment deployments | Parallel pipelines, rollback |
| Enterprise | Governance | Self-hosted, access controls |
| Healthcare | Regulatory adherence | Approval workflows, SAST |
Fintech organisations face dual pressure: regulators require audit trails and policy-gated releases, while competitive dynamics demand release velocity. A CI/CD pipeline with built-in compliance gates resolves this tension without manual overhead.
Healthcare pipelines prioritise approval workflows and static application security testing (SAST) to meet HIPAA and similar regulatory requirements. SaaS organisations running multi-tenant infrastructure need parallel pipelines and reliable rollback to maintain availability while deploying frequently across multiple environments.
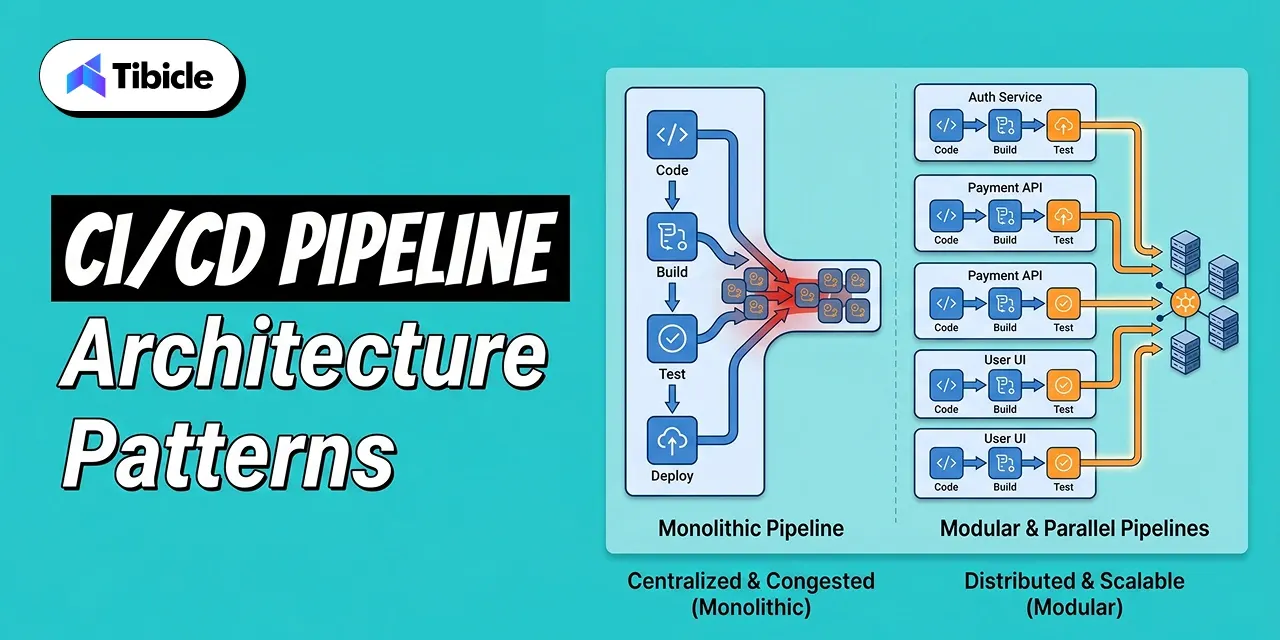
CI/CD Pipeline Architecture Patterns
Pipeline architecture decisions made early are difficult and expensive to reverse. The pattern you choose must align with your current codebase structure and the scale you expect to reach.
Monolithic vs. Microservices-Native CI/CD Pipeline Architecture
Monolithic pipelines run a single, sequential flow for the entire codebase. Although they are simple to configure and maintain at small scale, but they break under growth: one failing service blocks the pipeline for every other service. A change to a low-risk utility component triggers the same full test suite as a change to a core payment service, wasting execution time and slowing feedback.
Parallel and modular pipelines isolate changes per service or component. In practice, each microservice has its own pipeline definition changes that trigger only the relevant pipeline, reducing total execution time and limiting blast radius when failures occur. This pattern is essential for organisations running more than 10 independent services.
GitOps extends CI/CD pipeline automation to infrastructure through infrastructure as code practices. Configuration is declared in Git repositories, and deployments are triggered by commits to those repositories. The result is an auditable, reversible infrastructure delivery process every change has a git commit, every deployment has an approval record, and rollback is a git revert.
AI-Assisted CI/CD Pipeline Automation in 2026
AI integration in CI/CD pipeline tooling has moved from experimental to production-ready. AI agents now diagnose flaky tests, identify the root cause of build failures, predict which tests are most likely to catch regressions for a given code change, and recommend remediation before developers manually investigate. Harness uses machine learning models to verify deployments and detect post-release anomalies flagging issues before they escalate into incidents. This capability reduces mean time to recovery (MTTR) and limits the engineering time spent on reactive investigation.
Tool Comparison Pricing and Use-Case Fit
Selecting the right CI/CD pipeline platform requires evaluating more than the headline feature list. In particular, pricing models, hosting requirements, ecosystem fit, and total cost of ownership all vary significantly across vendors. The table below provides a baseline comparison across the leading platforms.
| Quick Tool Summary | |
| GitHub Actions: | A CI/CD automation tool built natively into GitHub that triggers workflows on every commit or pull request. |
| GitLab CI/CD: | An integrated pipeline automation layer within the GitLab DevOps platform covering source control, testing, and deployment. |
| Jenkins: | An open-source automation server for building custom, self-hosted CI/CD pipelines with full configuration control. |
| CircleCI: | A cloud-based pipeline automation platform optimised for build speed, parallelisation, and Docker-native workflows. |
| Azure DevOps: | Microsoft’s end-to-end DevOps pipeline suite tightly integrated with Azure cloud infrastructure and the Microsoft toolchain. |
| Harness: | An AI-assisted software delivery platform that uses machine learning to verify deployments and automate rollback decisions. |
| Tool | Pricing (Approx.) | Best For | Hosting Model | Maintenance Burden |
| GitHub Actions | Free tier; $0.008 $0.16/min (runners) | GitHub-native teams | Cloud | Low |
| GitLab CI/CD | $29 $99/user/month | All-in-one DevOps | Cloud / Self-hosted | Low-Medium |
| Jenkins | $0 license + infra | Custom enterprise needs | Self-hosted | High |
| CircleCI | $15/month + credits | Build speed priority | Cloud / Self-hosted | Low |
| Azure DevOps | $6/user/month | Microsoft-stack teams | Cloud | Low |
| Harness | Custom enterprise pricing | AI-verified deployments | Cloud | Low-Medium |
Total Cost of Ownership What the CI/CD Pipeline Sticker Price Does Not Show
However, licence cost is the least reliable metric for comparing CI/CD pipeline platforms. The real cost calculation must account for infrastructure, maintenance engineering time, migration effort, and the opportunity cost of pipeline downtime:
- Jenkins is open-source, but teams running Jenkins pipelines spend 5 to 10 hours per week on maintenance configuration management, plugin updates, security patching, and infrastructure upkeep. DORA research estimates this at $15,000 to $30,000 annually in engineering time for a mid-size team, making Jenkins one of the more expensive platforms despite its zero-license cost.
- GitHub Actions pipeline pricing scales with usage. However, the per-minute runner cost is modest for small teams but compounds quickly for larger organisations running frequent builds across many repositories. A team of 50 engineers running 200 pipeline executions per day can generate substantial monthly spend before factoring in storage costs.
- For a 10-developer team as a benchmark: GitLab Premium runs approximately $290 per month. CircleCI Performance starts at $15 per month plus usage credits, which scales with build volume. Jenkins, factoring in infrastructure and maintenance overhead, typically costs $400 to $800 per month in total, significantly more than its zero-license price suggests.
Running a CI/CD audit for your team? Tibicle’s engineers can benchmark your current pipeline against DORA metrics and identify where you’re losing speed or taking on unnecessary risk. Book a free consultation.
ROI of a Well-Built Pipeline
Consequently, the return on a properly implemented CI/CD pipeline shows up across multiple business metrics simultaneously, not just engineering throughput. Organisations implementing CI/CD practices report a 50% increase in the ability to experiment and innovate, according to CA Technologies and Broadcom research. That capacity for controlled experimentation has direct product and revenue implications: teams that can safely test and ship features faster than competitors respond to market signals with greater agility.
Higher deployment frequency and lower mean time to recovery (MTTR) reduce downtime costs and compress the cycle between identifying a production issue and resolving it. After all, every hour of downtime carries financial cost lost revenue, support overhead, reputational impact. A CI/CD pipeline with automated rollback and real-time monitoring shrinks that window.
How to Measure CI/CD Pipeline ROI Using DORA Metrics
DORA metrics, developed through the DevOps Research and Assessment programme, provide the most widely accepted measurement framework for CI/CD pipeline performance. The four key metrics are:
- Deployment frequency: How often your organisation successfully releases to production. Elite performers deploy on-demand, multiple times per day. Low performers deploy monthly or less.
- Lead time for changes: The time from code commit to code running in production. Shorter lead times indicate a more efficient CI/CD pipeline.
- Change failure rate: The percentage of deployments that cause a production incident. A mature CI/CD pipeline with strong automated testing keeps this below 15%.
- Mean time to recovery (MTTR): How long it takes to restore service after a production failure. MTTR below one hour is an indicator of a high-performing delivery organisation.
ROI calculation framework: (Cost of failed deliveries + Productivity gain) minus (Solution cost + Overhead + Training cost), divided by total investment. Applying this formula using your actual deployment failure rate, average incident cost, and current engineering utilisation yields a specific, defensible ROI figure for stakeholder presentations.
What Poor CI/CD Pipeline Performance Actually Costs
The cost of an underperforming CI/CD pipeline is distributed across the organisation in ways that are easy to miss in budget reviews:
- 63% of CI/CD pipeline failures stem from resource exhaustion, according to the Datadog 2024 DevOps Report. Pipelines failing due to infrastructure limits generate both direct costs (re-runs, delayed releases) and indirect costs (developer context-switching, investigation time).
- Similarly, slow builds create compound developer friction. A developer waiting 30 minutes for a pipeline run instead of 5 minutes loses 25 minutes of productive capacity per cycle. Multiplied across daily commits and team size, this idle time represents significant engineering budget spent on non-output.
- Production bug fix costs run 6 to 10 times higher than catching the same defect in automated testing within the CI/CD pipeline. The financial argument for investing in test coverage and pipeline robustness is straightforward: prevention is materially cheaper than remediation.
Risks and Implementation Challenges
A CI/CD pipeline that moves fast without adequate security controls, scalability planning, or organisational alignment introduces risks that can outweigh the velocity benefits. Therefore, engineering leaders need to plan for four categories of failure.
Security Gaps at CI/CD Pipeline Speed
Furthermore, speed without security controls creates an attack surface that compounds with every release cycle:
- Open-source dependencies introduce supply chain vulnerabilities at the point of integration. Software Composition Analysis (SCA) scanning within the CI/CD pipeline identifies vulnerable dependencies before they reach staging environments.
- Furthermore, hardcoded secrets in configuration files, environment variable definitions, and pipeline scripts remain a leading attack vector. Secrets management tools HashiCorp Vault, AWS Secrets Manager provide centralised, auditable credential storage that eliminates hardcoded credentials from pipeline definitions.
- DevSecOps integration shifts security testing left SAST, DAST, and dependency scanning run inside the CI/CD pipeline, not after it. This approach catches vulnerabilities when remediation cost is lowest and prevents security review from becoming a deployment bottleneck.
Scalability Bottlenecks in CI/CD Pipeline Architecture
As a result, monolithic pipeline architectures degrade predictably as microservices proliferate. A single service change triggering a full pipeline run for a 30-service application is both slow and wasteful. Pipeline architecture should be designed for the scale you expect to reach, not just the scale you operate at today.
SaaS platforms scaling across users, data volume, and third-party integrations require CI/CD pipelines built for horizontal growth parallelisation, modular pipeline definitions, and infrastructure that scales compute on demand.
Compliance and Audit Failures in CI/CD Pipeline Governance
Removing manual approval gates in the pursuit of speed creates accountability gaps in regulated industries. When a pipeline deploys directly to production without a human review record, audit requirements become difficult to satisfy particularly in financial services and healthcare.
GitOps and policy-as-code frameworks enforce compliance automatically through the CI/CD pipeline without slowing release velocity. Policy definitions codified in Git provide auditable change records. Deployment gates enforced by code rather than by individual approvers scale consistently across services and environments.
Cultural and Organisational Readiness for CI/CD Pipeline Adoption
The most underestimated CI/CD pipeline implementation risk is organisational. In practice, a well-configured pipeline installed into a team without developer buy-in, documented runbooks, or leadership visibility into pipeline health defaults back to manual workarounds within 60 to 90 days. Engineers route around automation they do not trust or understand.
Successful CI/CD pipeline adoption requires: clear ownership of pipeline configuration and maintenance, visible pipeline metrics accessible to engineering leadership, documented incident response procedures for pipeline failures, and onboarding processes that build developer confidence in the automated system before eliminating manual safety nets.
Vendor Selection Checklist
Use this checklist before shortlisting any CI/CD pipeline platform. Each question surfaces a requirement category that commonly drives platform regret when ignored during evaluation:
- Does it integrate natively with your current version control system GitHub, GitLab, or Bitbucket?
- What are your data residency requirements? Does a cloud-hosted CI/CD pipeline comply, or do regulations require a self-hosted deployment?
- Does it support your deployment targets Kubernetes clusters, serverless functions, multi-cloud environments, or hybrid on-premise and cloud infrastructure?
- What is the realistic total cost of ownership, including infrastructure, maintenance engineering time, and training not just the licence fee?
- Does it support parallel builds and intelligent test splitting at the scale your team operates today and expects to reach within 24 months?
- Are SAST, DAST, and SCA scanning capabilities built into the platform or bolted on as third-party integrations requiring separate licensing and configuration?
- What observability integrations are available Prometheus, Grafana, Datadog and how deeply do they integrate with the pipeline rather than just consuming its output?
- Does it support advanced CI/CD pipeline deployment strategies: blue-green, canary, and rolling deployments with automated rollback?
- How complex and costly is migration if you outgrow the platform? What does the data portability story look like?
- What SLA does the vendor offer for CI/CD pipeline uptime, and what is the documented support response time for critical failures?
Top CI/CD Tools in 2026 Quick Reference
For organisations finalising a CI/CD pipeline platform shortlist, the following profiles provide a rapid comparison based on primary use-case fit:
- GitHub Actions: Best CI/CD pipeline choice for teams already on GitHub. Lowest setup friction, native integration with the most widely used version control platform, and a large library of community-maintained actions.
- GitLab CI/CD: Best all-in-one CI/CD pipeline option. Covers source control, CI/CD automation, and security scanning in a single platform eliminating the integration overhead of assembling separate tools.
- Jenkins: Best CI/CD pipeline solution for custom, self-hosted enterprise environments requiring full configuration control. Carries the highest maintenance burden but offers maximum extensibility.
- CircleCI: Best raw build speed among cloud-hosted CI/CD pipeline platforms. Strong Docker support and parallelisation capabilities make it a strong choice for teams where build duration is the primary constraint.
- Azure DevOps: Best CI/CD pipeline platform for Microsoft-aligned organisations. Integrates tightly with Azure infrastructure, Active Directory, and the Microsoft development toolchain.
- Harness: Best CI/CD pipeline option for teams requiring AI-assisted deployment verification and automated rollback. The ML-based deployment verification layer reduces the manual investigation load after each production release.
Why Tibicle LLP Is Worth Considering for CI/CD Pipeline Implementation
Most CI/CD pipeline failures are not tool failures. They are architecture failures, configuration failures, or adoption failures. The platform chosen rarely causes the problem of how it is designed, integrated, and embedded into team workflows determines whether a CI/CD pipeline delivers compounding value or recurring operational friction.
Tibicle focuses on designing CI/CD pipelines that align with your existing technology stack rather than requiring a wholesale replacement. This approach reduces implementation risk, shortens time to value, and avoids the disruption of migrating live systems during a transformation initiative.
Where Tibicle Fits in Your CI/CD Pipeline Decision
- Custom CI/CD pipeline architecture for complex or legacy technology stacks where standard platform documentation does not address your specific deployment constraints.
- DevSecOps integration security built into the CI/CD pipeline from day one, not retrofitted after an incident.
- Support for multi-cloud, hybrid, and microservices-native delivery environments requiring pipeline architectures that span infrastructure boundaries.
- Ongoing CI/CD pipeline performance audits using DORA metrics as the baseline identifying where deployment frequency, lead time, change failure rate, or MTTR are underperforming relative to industry benchmarks.
See how Tibicle’s CI/CD pipeline implementation approach compares to your current setup. Book a Call to discuss your architecture, stack, and delivery objectives.
Conclusion
A CI/CD pipeline is a software delivery pipeline with measurable financial and operational implications not a technical configuration to delegate entirely to an engineering team. The platform you select, the architecture you build, and the metrics you track determine whether a CI/CD pipeline becomes a genuine competitive advantage or a recurring source of downtime, security exposure, and wasted engineering hours.
The decision deserves the same rigour applied to any significant infrastructure investment: clear requirements, honest total cost analysis, and an honest assessment of organisational readiness not just technical readiness for the change.
Talk to Tibicle LLP’s engineering team to audit your current CI/CD pipeline, benchmark it against DORA standards, and identify where you are leaving speed and reliability on the table. Schedule Your Pipeline Review.
Frequently Asked Questions About CI/CD Pipelines
What is the difference between CI and CD in a CI/CD pipeline?
CI handles automatic code integration and testing on each commit. CD manages releases to staging (Continuous Delivery) or production (Continuous Deployment). The main difference is whether a production release needs manual approval or runs automatically.
How long does it take to set up a CI/CD pipeline?
Cloud tools like GitHub Actions or CircleCI can be set up in a few days. Jenkins usually takes 2-4 weeks. Enterprise setups with compliance and multiple environments can take 1 3 months.
What is the average cost of a CI/CD pipeline for a mid-size team?
For 10 developers: GitLab Premium is about $290/month. CircleCI starts at $15/month plus usage. Jenkins is free but typically costs $400 $800/month with infrastructure and maintenance.
How do you measure the ROI of a CI/CD pipeline?
Use DORA metrics: deployment frequency, lead time, failure rate, and MTTR. ROI = (failure cost + productivity gain − total costs) ÷ total investment.
What are the biggest security risks in a CI/CD pipeline?
Key risks include hardcoded secrets, vulnerable dependencies, and weak access control. Reduce risk with SAST, DAST, SCA, and proper secrets management tools.
Written by
Recent Blogs
What Is a Product Roadmap? The Complete Guide for 2026
Introduction Your product roadmap is the document everyone references and almost no one trusts. According to Airtable’s 2025 Predictions Report, 92% of product leaders are directly responsible for revenue outcomes, yet only 26% have high visibility into the ROI of their launches. That gap does not come from weak strategies. It comes from roadmaps that […]
Cross-Platform App Development Guide for All Businesses
Introduction The global cross-platform app development software market grew from $104.6 billion in 2025 to nearly $121 billion in 2026, expanding at a 15.7% CAGR as businesses accelerate mobile-first transformation strategies. For many organizations, building separate native applications for iOS and Android no longer makes financial or operational sense because it doubles engineering effort, increases […]

eCommerce App Features That Increase Sales in 2026
Introduction eCommerce app features are becoming the biggest factor behind mobile commerce growth in 2026, where mobile eCommerce is projected to account for approximately 73% of all global eCommerce sales. Despite this significant traffic dominance, the average mobile app currently converts at under 2%, while desktop conversion rates are closer to 3.9%. This disparity indicates […]
Got an Idea? Get FREE Consultation
In our world, there's no such thing as having too many clients






